Built for the team that owns this security review.
Security, data protection, compliance, and cloud teams that need a clearer picture of sensitive data, access risk, and reviewable control priorities.
 Tutelaby H2H
Tutelaby H2HData security
Data Security helps teams discover sensitive data, classify risk with business context, understand access paths, and prioritize the control decisions that matter most.
Help security teams move from scattered inventory to a clearer view of sensitive data, risky access, and the next protection decision.
Security, data protection, compliance, and cloud teams that need a clearer picture of sensitive data, access risk, and reviewable control priorities.
Sensitive data is spread across cloud environments, applications, and business workflows. Teams need to know what matters, who can reach it, and which controls should come first without drowning in raw inventory.
Data Security is designed for customer-owned environments. AWS Marketplace links are shown only when an approved listing URL is configured.
Prioritize sensitive data based on classification, access graph, exposure, and risk context
Prepare protection, tokenization, and retention decisions with reviewable evidence
Support security, compliance, and investigation conversations with clearer data context
Data Security helps teams understand where sensitive data lives, how risk should be classified, who can reach it, and which protection decisions deserve attention first.
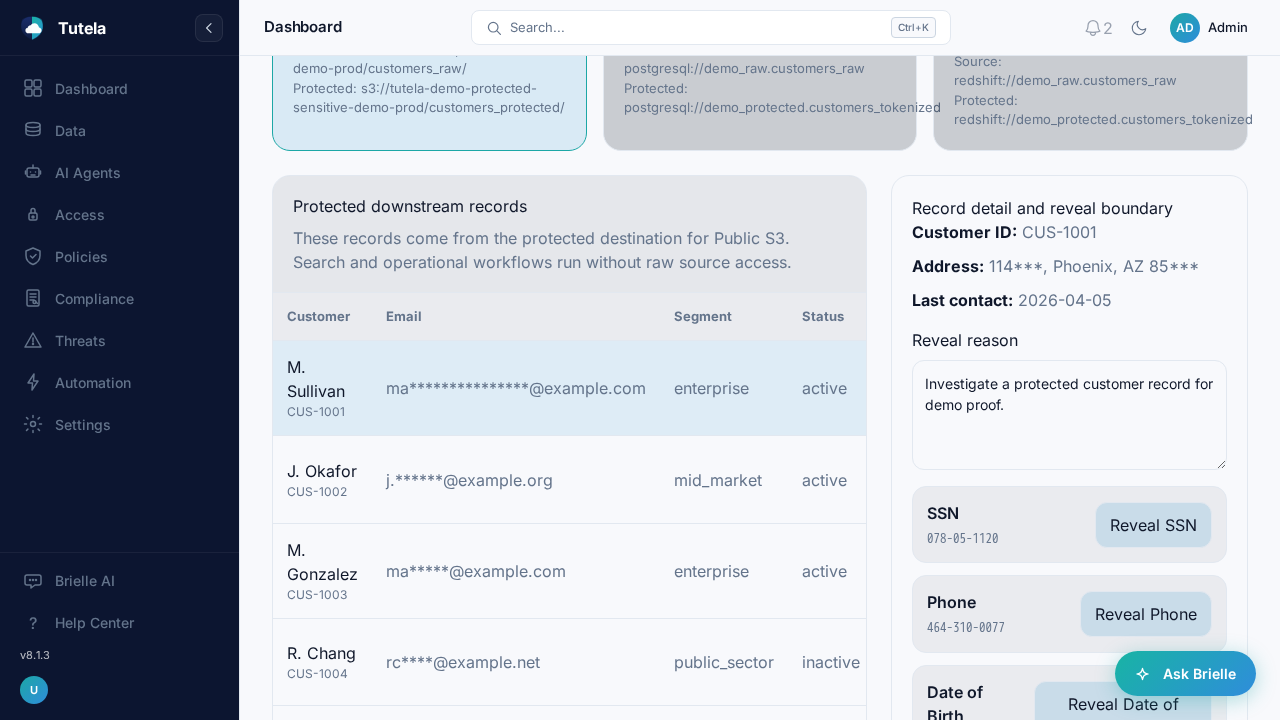
See masked downstream records, governed reveal controls, and the context teams need before protected data is exposed.
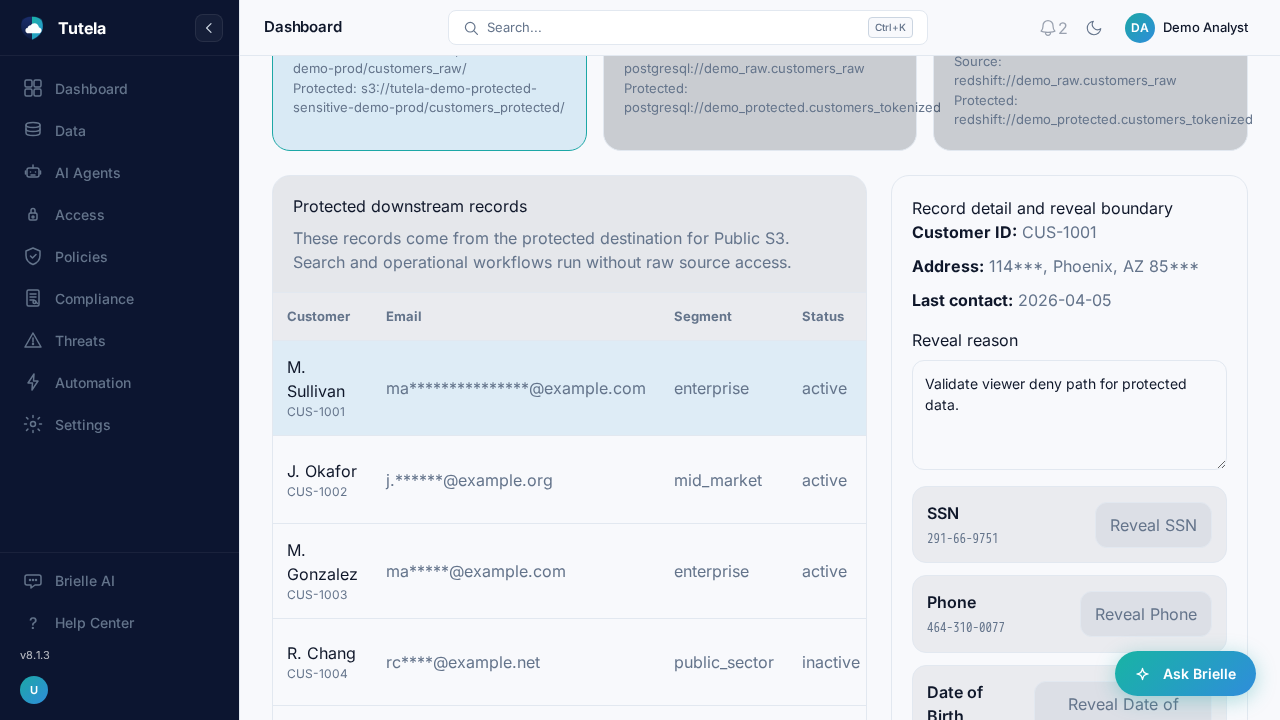
Show teams the deny state first so protected data is not casually revealed during operational review.
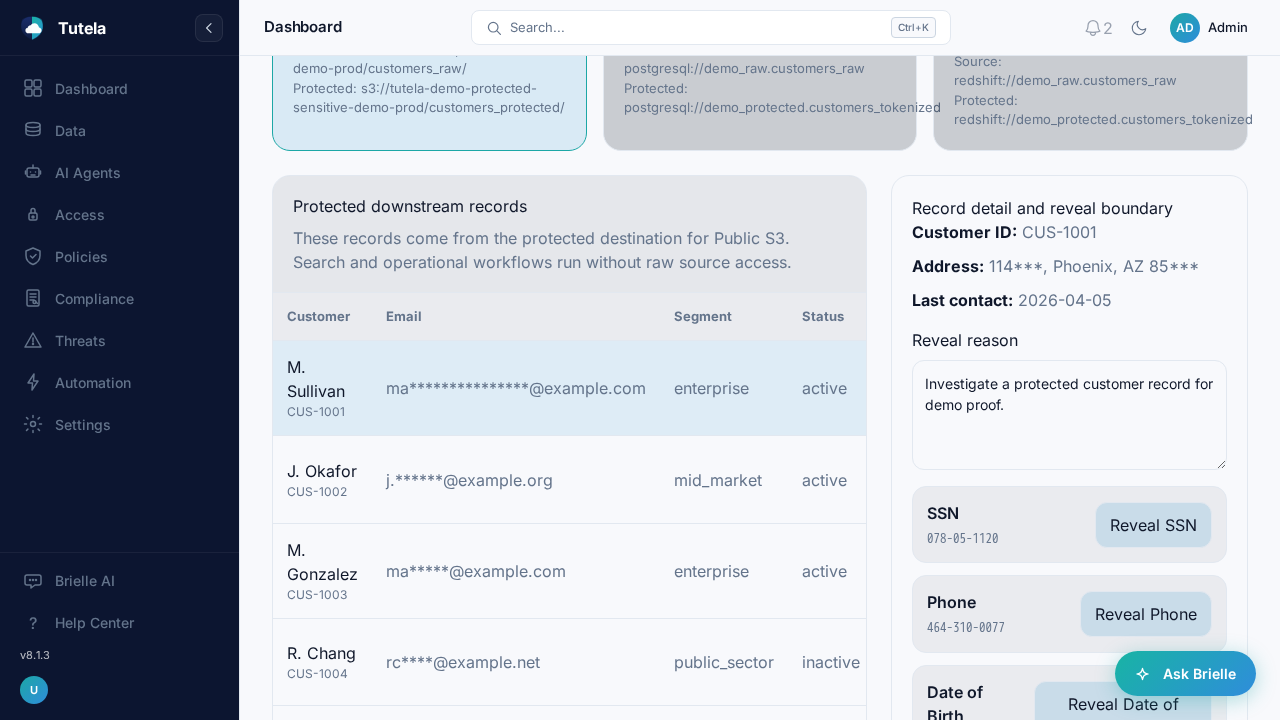
Move from masked records into a governed reveal boundary when a reviewer has the right context and approval.
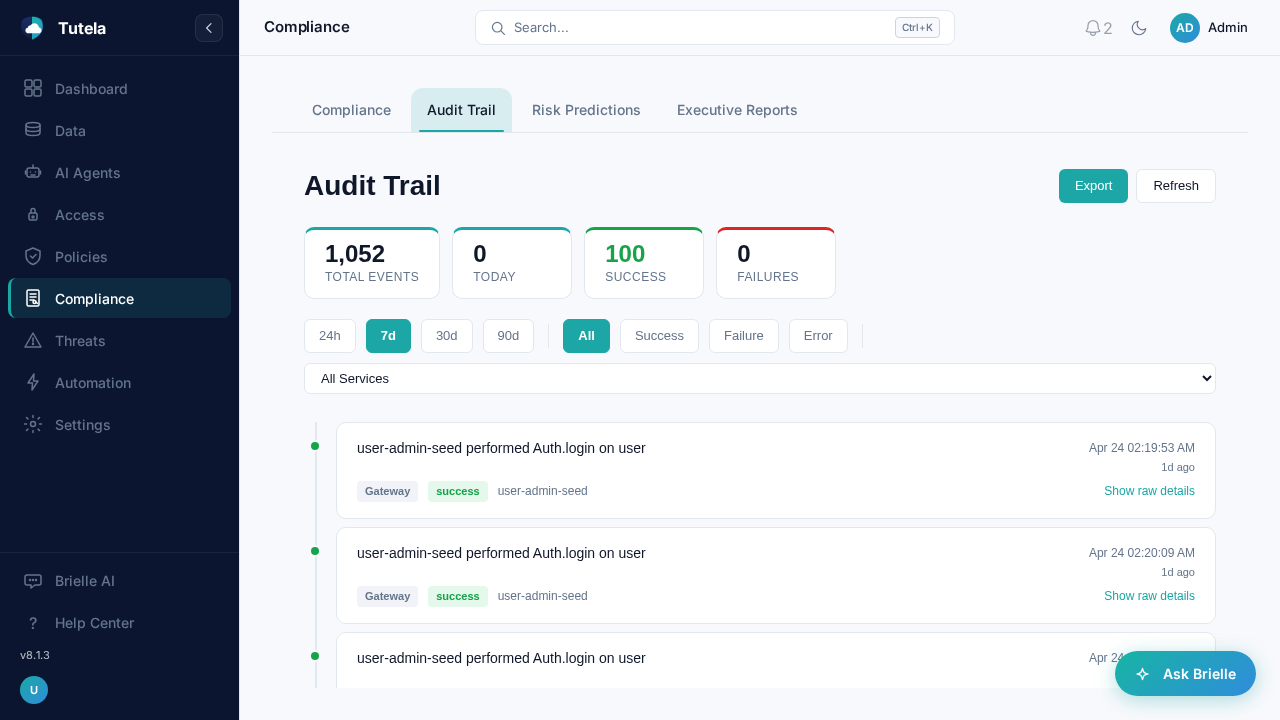
Preserve an audit trail that explains what was reviewed, which actions were taken, and why the decision was allowed.
Build a sensitive-data map that helps teams separate regulated, confidential, and business-critical data from ordinary inventory.
Connect sensitive-data context to access graph paths so exposure risk is easier to prioritize.
Use risk scoring to prepare protection, tokenization, and retention decisions around the data that matters most.
Keep review artifacts organized for security, compliance, and platform teams evaluating a customer-owned deployment.
Use the product page to understand what your team can inspect, compare, and discuss before moving into deeper technical material.
Where regulated, confidential, and business-critical data exists.
Who can reach high-risk data and which access paths matter most.
Which tokenization, protection, retention, and compliance decisions need review.
Find sensitive data across cloud and application paths without moving review ownership away from the customer.
Classify business and regulatory context so data risk is not treated as a flat inventory problem.
Map access paths, permissions, exposure, and graph relationships that create practical risk.
Prepare tokenization, protection, and retention decisions around the data that matters most.
Organize review evidence security, compliance, and platform teams can use before deployment.
Tutela is designed for customer-owned deployment. Use the architecture and readiness material to understand operating boundaries without turning deployment mechanics into the whole product story.
Designed for environments where sensitive data discovery, access context, and control planning should remain under customer ownership.
Connect cloud data paths, identity, application access, and classification context before choosing protection actions.
Use technical guides to prepare architecture, data ownership, and operating responsibilities before production use.
These questions help buyers decide whether this product fits the problem in front of them and which resource to read next.
Prioritize sensitive data based on classification, access graph, exposure, and risk context
Prepare protection, tokenization, and retention decisions with reviewable evidence
Support security, compliance, and investigation conversations with clearer data context
Prioritize sensitive data based on classification, access graph, exposure, and risk context
Data Security, Agentic Security, and Exposure Validation solve different questions in the same operating model. Use the portfolio overview when your team needs to compare the modules side by side.
Data Security gives teams the sensitive-data map, classification context, and access insight that often clarifies where Agentic Security should focus next.
Compare the products side by side if the problem shifts from data discovery to AI workflow governance, or from product fit to posture validation.
Compare ProductsUse these resources when your team is ready to move from public product fit into the next useful technical or planning conversation.
Leadership-facing overview of sensitive-data posture, access risk, and control priorities before deeper technical review.
Who should read this next: Security leaders, data-risk owners, and cross-functional buyers reviewing sensitive-data posture and control priorities.
Open the overviewA Data Security-specific architecture brief for teams reviewing sensitive-data discovery, business context, access analysis, and protection planning.
Who should read this next: Teams evaluating sensitive data discovery, classification, access graph, and control planning.
Open the briefA deployment-readiness guide for teams preparing identity, secrets, support-path, and ownership questions before a customer-owned rollout.
Who should read this next: Cloud, security, and operations teams preparing customer-owned deployment review.
Open the guideIt helps teams discover sensitive data, classify business and regulatory risk, and understand where protected information exists across cloud and application paths.
It connects sensitive-data context with access analysis so teams can see who can reach data, how access is created, and where protection decisions should come first.
Data Security supports tokenization, protection, and retention decisions by giving security and data teams a clearer view of the data that needs control.
Tutela products are designed for customer-owned deployment so sensitive-data review can stay under the customer's operating control.
Data Security establishes the sensitive-data map and access context that Agentic Security can use when teams govern employee AI use and AI workflow risk.
Explore the architecture, deployment, and planning material that helps your team decide whether to go deeper.